CryptBot Malware Analysis

Overview
CryptBot is a Windows-based Trojan malware first discovered in the wild in December 2019. It belongs to the prolific category of information stealers, whose primary objective is to gather sensitive data from infected devices and exfiltrate it to threat actors. This includes credentials, cryptocurrency wallets, browser data, and system information.
According to a detailed report from Darktrace, CryptBot draws inspiration from earlier infostealers like ZeuS (discovered in 2006). After ZeuS's source code leaked, variants proliferated, and infostealers have since become a staple in cybercrime. In recent months, SOC (Security Operations Center) teams have observed multiple infections across customer bases involving similar stealers.
Key characteristics of CryptBot:
- Distribution Methods: Often spread via cracked software, fake updates, or malvertising campaigns.
- Capabilities: Steals browser cookies, saved passwords, cryptocurrency wallet data, screenshots, and keystrokes. It also checks for admin privileges and God Mode in Windows.
- Evasion Techniques: Uses packing, string encryption, and dynamic configuration to avoid detection.
- Impact: Targets individuals and organizations for financial gain, often leading to identity theft or ransomware follow-ups.
Analysis
Activities
Activity Dynamics
The following graph illustrates the dynamic behavior of CryptBot during infection, including initial execution, data collection, and exfiltration phases. The data took from MalwareHunter's infographic.
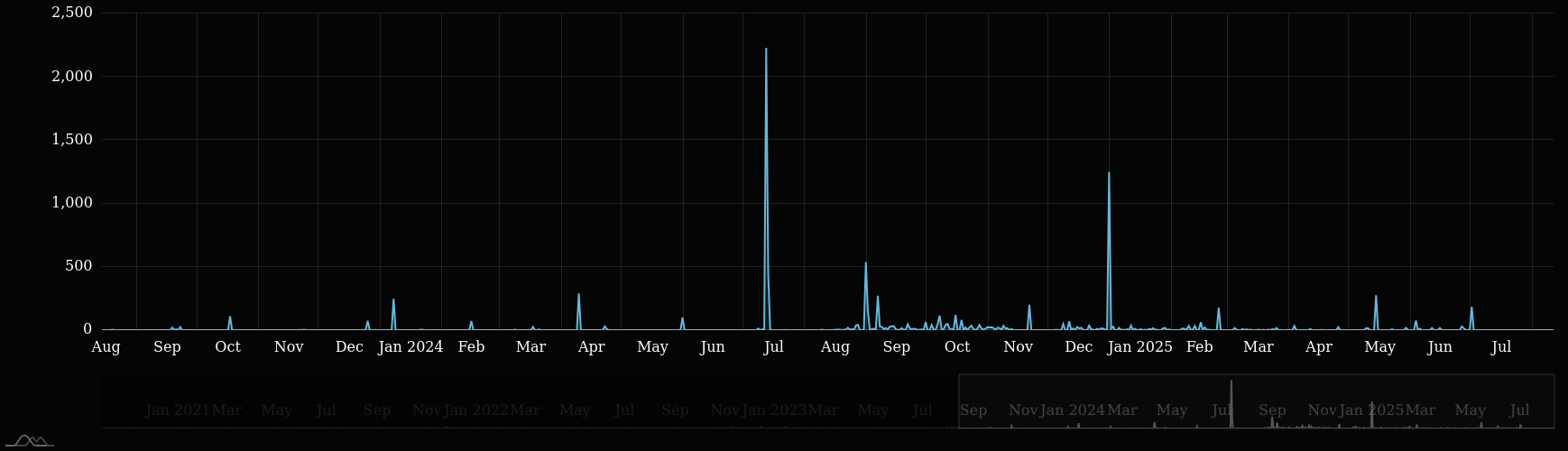
Malicious Infrastructure Growth Dynamics
This detailed graph shows the growth of CryptBot's command-and-control (C2) infrastructure over time, highlighting domain registrations and IP changes.

- Trends: Rapid domain cycling to avoid blacklisting.
- Indicators: High volume of short-lived domains like
.topTLDs.
Programming Language
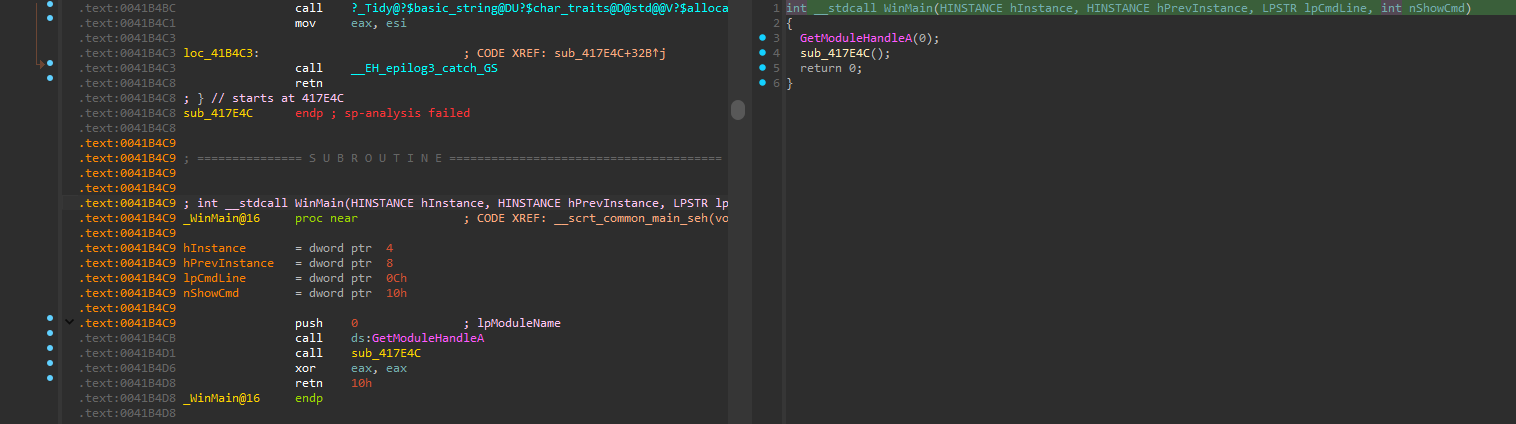
Based on the unpacked sample and the function declarations, revealed during the analysis by IDA Pro, the malware is written in C/C++. This is evident from low-level API calls, string handling, and memory management patterns observed in the disassembled code.
Static Analysis
Static analysis reveals CryptBot's configuration parsing, string obfuscation, and data theft routines. The malware uses UTF-16LE encoded strings and bracketed formats like [<Variable>] for config variables (e.g., [<Bitcoin>] for wallet data).
Configuration Parsing Snippet
Here's a NASM snippet showing config parsing. Note the use of bracketed tags for variables like Process, Screenshot, and Key.
nasm1.rdata:004AC220 asc_4AC220: ; DATA XREF: sub_417E4C+142A↑o 2.rdata:004AC220 text "UTF-16LE", '[<',0 3.rdata:004AC226 aProcess db 'Process:',0 4.rdata:004AC22F align 10h 5.rdata:004AC230 text "UTF-16LE", '>]',0 6.rdata:004AC236 align 4 7.rdata:004AC238 a1: ; DATA XREF: sub_417E4C:loc_41934E↑o 8.rdata:004AC238 ; sub_4599AD+3B↑o ... 9.rdata:004AC238 text "UTF-16LE", '1',0 10.rdata:004AC23C align 10h 11.rdata:004AC240 asc_4AC240: ; DATA XREF: sub_417E4C+1592↑o 12.rdata:004AC240 text "UTF-16LE", '[<',0 13.rdata:004AC246 aScreenshot db 'Screenshot',0 14.rdata:004AC251 align 2 15.rdata:004AC252 db '>',0 16.rdata:004AC254 db ']',0 17.rdata:004AC256 align 4 18.rdata:004AC258 a2 db '2',0 ; DATA XREF: sub_417E4C:loc_41941B↑o 19.rdata:004AC25A align 10h 20.rdata:004AC260 asc_4AC260: ; DATA XREF: sub_417E4C+166D↑o 21.rdata:004AC260 text "UTF-16LE", '[<',0 22.rdata:004AC266 aKey_0 db 'Key',0 23.rdata:004AC26A db 0 24.rdata:004AC26B db 3Eh ; > 25.rdata:004AC26C db 0 26.rdata:004AC26D db 5Dh ; ] 27.rdata:004AC26E db 0 28.rdata:004AC26F db 0
- Explanation: These strings are used to tag stolen data in exfiltrated payloads. The malware constructs formatted output like
[<Process:>]before sending.
Privilege Checks
The malware checks for Windows God Mode (a hidden feature for advanced settings) and admin privileges.
God Mode is a (clearly exaggerated) term for a folder that contains links to all kinds of system settings directly on your desktop (or wherever you choose to create it). Despite its intimidating name, God Mode is very easy to set up, and there's almost no risk to it, aside from making important settings easily accessible. {: .prompt-info }
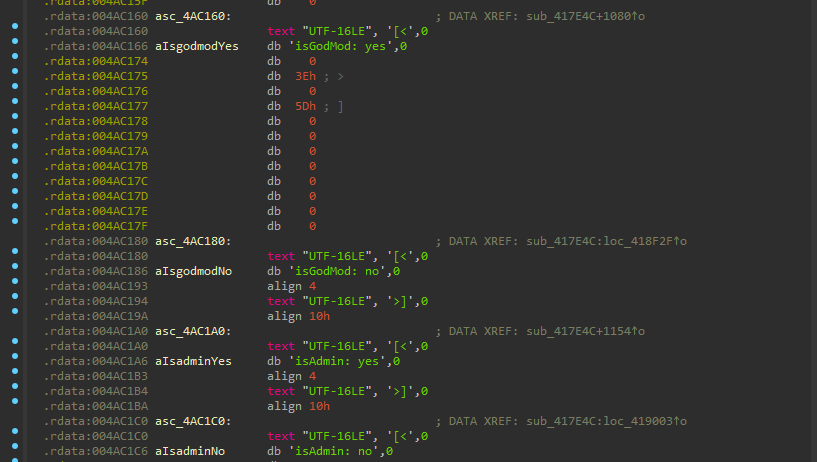
- God Mode Check: References to
GodMode.{ED7BA470-8E54-465E-825C-99712043E01C}indicate attempts to access elevated features. - Admin Check: Uses API calls like
IsUserAnAdmin()to determine escalation needs.
Interesting Strings (Wallet Extensions)
CryptBot targets crypto wallets via browser extensions. Here's a snippet showing hardcoded extension IDs and names.
nasm1.rdata:004A43F0 asc_4A43F0: ; DATA XREF: sub_401000+1E↑o 2.rdata:004A43F0 ; sub_401887+1E↑o ... 3.rdata:004A43F0 text "UTF-16LE", '[<',0 4.rdata:004A43F6 aFhbohimaelbohp db 'fhbohimaelbohpjbbldcngcnapndodjp',0 ; Extension ID for a wallet 5.rdata:004A4417 align 4 6.rdata:004A4418 text "UTF-16LE", '>]',0 7.rdata:004A441E align 10h 8.rdata:004A4420 asc_4A4420: ; DATA XREF: sub_401000+28↑o 9.rdata:004A4420 ; sub_4011E0+134↑o ... 10.rdata:004A4420 text "UTF-16LE", '[<',0 11.rdata:004A4426 aGuarda db 'Guarda',0 ; Wallet name: Guarda 12.rdata:004A442D align 2 13.rdata:004A442E db '>',0 14.rdata:004A4430 db ']',0 15.rdata:004A4432 align 10h 16.rdata:004A4440 asc_4A4440: ; DATA XREF: sub_401000+32↑o 17.rdata:004A4440 ; sub_401887+32↑o ... 18.rdata:004A4440 text "UTF-16LE", '[<',0 19.rdata:004A4446 aHpglfhgfnhbgpj db 'hpglfhgfnhbgpjdenjgmdgoeiappafln',0 ; Extension ID 20.rdata:004A4467 align 4 21.rdata:004A4468 text "UTF-16LE", '>]',0 22.rdata:004A446E align 10h 23.rdata:004A4470 asc_4A4470: ; DATA XREF: sub_401000+3C↑o 24.rdata:004A4470 ; sub_401887+3C↑o ... 25.rdata:004A4470 text "UTF-16LE", '[<',0 26.rdata:004A4476 aCoin98 db 'Coin98',0 ; Wallet name: Coin98 27.rdata:004A447D align 2 28.rdata:004A447E db '>',0 29.rdata:004A4480 db ']',0 30.rdata:004A4482 align 10h 31.rdata:004A4490 asc_4A4490: ; DATA XREF: sub_401000+46↑o 32.rdata:004A4490 ; sub_401887+46↑o ... 33.rdata:004A4490 text "UTF-16LE", '[<',0 34.rdata:004A4496 aAeachknmefphep db 'aeachknmefphepccionboohckonoeemg',0 ; Extension ID 35.rdata:004A44B7 align 4 36.rdata:004A44B8 text "UTF-16LE", '>]',0 37.rdata:004A44BE align 10h 38.rdata:004A44C0 asc_4A44C0: ; DATA XREF: sub_401000+50↑o 39.rdata:004A44C0 ; sub_401190+14↑o ... 40.rdata:004A44C0 text "UTF-16LE", '[<',0 41.rdata:004A44C6 aMath db 'Math',0 ; Wallet name: Math 42.rdata:004A44CB align 4 43.rdata:004A44CC text "UTF-16LE", '>]',0 44.rdata:004A44D2 align 10h 45.rdata:004A44E0 asc_4A44E0: ; DATA XREF: sub_401000+5A↑o 46.rdata:004A44E0 ; sub_401887+5A↑o ... 47.rdata:004A44E0 text "UTF-16LE", '[<',0 48.rdata:004A44E6 aAfbcbjpbpfadlk db 'afbcbjpbpfadlkmhmclhkeeodmamcflc',0 ; Extension ID 49.rdata:004A4507 align 4 50.rdata:004A4508 text "UTF-16LE", '>]',0 51.rdata:004A450E align 10h 52.rdata:004A4510 asc_4A4510: ; DATA XREF: sub_401000+64↑o 53.rdata:004A4510 ; sub_401887+64↑o ... 54.rdata:004A4510 text "UTF-16LE", '[<',0 55.rdata:004A4516 aTronlink db 'TronLink',0 ; Wallet name: TronLink 56.rdata:004A451F align 10h 57.rdata:004A4520 text "UTF-16LE", '>]',0 58.rdata:004A4526 align 10h 59.rdata:004A4530 asc_4A4530: ; DATA XREF: sub_401000+6E↑o 60.rdata:004A4530 ; sub_401887+6E↑o ... 61.rdata:004A4530 text "UTF-16LE", '[<',0 62.rdata:004A4536 aIbnejdfjmmkpcn db 'ibnejdfjmmkpcnlpebklmnkoeoihofec',0 ; Extension ID 63.rdata:004A4557 align 4 64.rdata:004A4558 text "UTF-16LE", '>]',0 65.rdata:004A455E align 10h 66.rdata:004A4560 asc_4A4560: ; DATA XREF: sub_401000+78↑o 67.rdata:004A4560 ; sub_401887+78↑o ... 68.rdata:004A4560 text "UTF-16LE", '[<',0 69.rdata:004A4566 aKeplr db 'Keplr',0 ; Wallet name: Keplr
- Explanation: These are bracketed tags for stealing data from specific wallets. The extension IDs correspond to Chrome Web Store entries. For example,
ibnejdfjmmkpcnlpebklmnkoeoihofecis TronLink's ID.
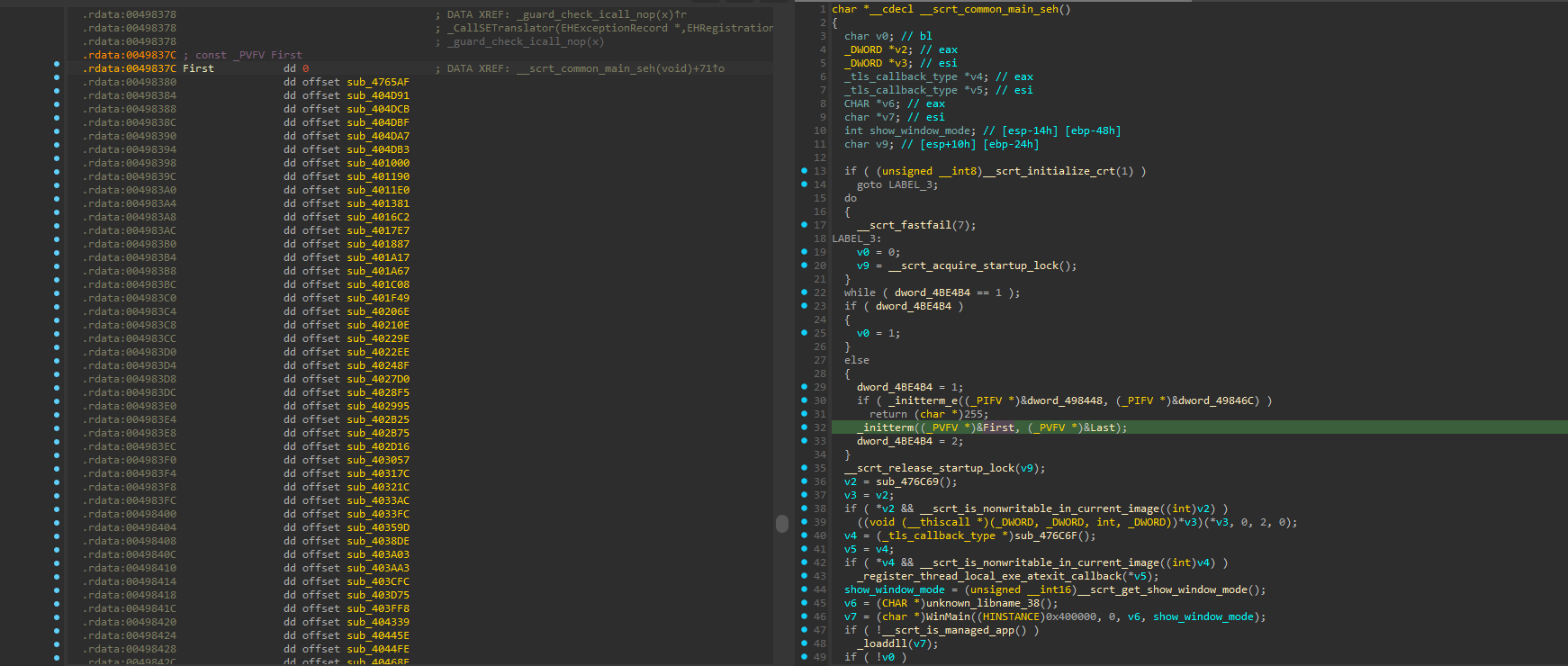
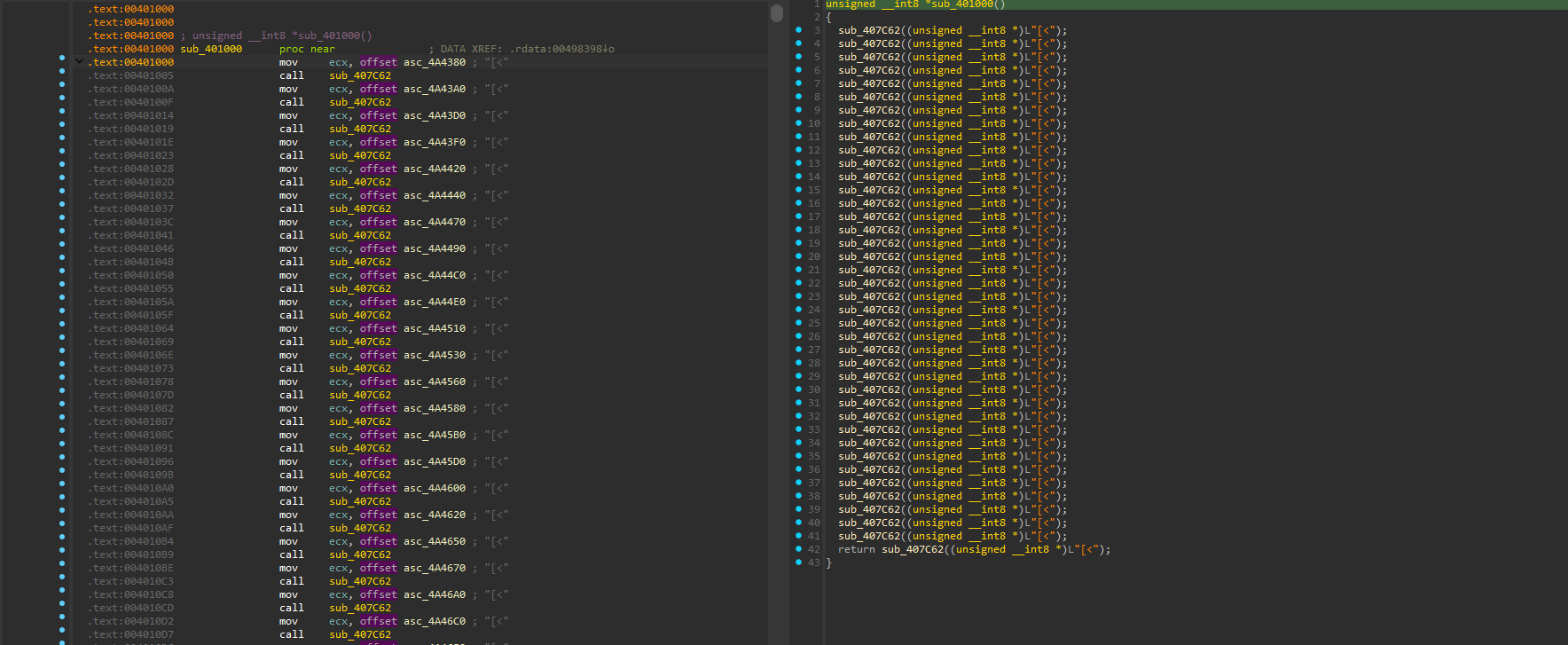
Initialization and Global Setup
The malware uses _initterm for initialization. Declarations reference multiple subroutines for setup.
- Renaming for Clarity:
sub_401000renamed tomw_setup_stealer_stringsas it handles string setup for theft. This will be reflected in the code snippets below during the analysis.
Check functions retrieving globals:
The content type appears to be a struct for caching strings:
c1unsigned __int8 *__thiscall sub_407C62(unsigned __int8 *this) 2{ 3 _BYTE *v2; // ebx 4 _BYTE *v3; // esi 5 int v4; // eax 6 int v5; // ecx 7 int v6; // esi 8 9 if ( *this == 0x5B ) 10 return this + 6; 11 if ( !dword_4BEF24 || !dword_4BEF20 ) 12 sub_407B97(); 13 v2 = malloc(__CFADD__(*this, 1) ? -1 : *this + 1); 14 v3 = malloc(5u); 15 *(_DWORD *)v3 = *(_DWORD *)(this + 1); 16 v3[4] = this[5]; 17 memmove_0(v2, this + 6, *this); 18 sub_407BF8((int)v2, *this); 19 v2[*this] = 0; 20 j___free_base(v3); 21 v4 = sub_407C22(v2); 22 v5 = dword_4BEF28; 23 v6 = dword_4BEF28; 24 if ( dword_4BEF28 < 0 ) 25 { 26LABEL_8: 27 *((_DWORD *)dword_4BEF24 + dword_4BEF28) = v4; 28 *(_DWORD *)(dword_4BEF20 + 4 * v5) = v2; 29 dword_4BEF28 = v5 + 1; 30 return v2; 31 } 32 else 33 { 34 while ( *((_DWORD *)dword_4BEF24 + v6) != v4 ) 35 { 36 if ( --v6 < 0 ) 37 goto LABEL_8; 38 } 39 j___free_base(v2); 40 return *(unsigned __int8 **)(dword_4BEF20 + 4 * v6); 41 } 42}
- Explanation: This function parses and caches bracketed strings, using malloc for dynamic allocation and hashing for quick lookups.
Back to initial declarations (NASM):
nasm1.rdata:0049837C First dd 0 ; DATA XREF: __scrt_common_main_seh(void)+71↑o 2.rdata:00498380 dd offset sub_4765AF 3.rdata:00498384 dd offset sub_404D91 4.rdata:00498388 dd offset sub_404DCB 5.rdata:0049838C dd offset sub_404DBF 6.rdata:00498390 dd offset sub_404DA7 7.rdata:00498394 dd offset sub_404DB3 8.rdata:00498398 dd offset mw_setup_stealer_strings 9.rdata:0049839C dd offset sub_401190 10.rdata:004983A0 dd offset sub_4011E0 11.rdata:004983A4 dd offset sub_401381 12.rdata:004983A8 dd offset sub_4016C2 13.rdata:004983AC dd offset sub_4017E7 14.rdata:004983B0 dd offset sub_401887 15.rdata:004983B4 dd offset sub_401A17 16.rdata:004983B8 dd offset sub_401A67 17.rdata:004983BC dd offset sub_401C08 18.rdata:004983C0 dd offset sub_401F49 19.rdata:004983C4 dd offset sub_40206E 20.rdata:004983C8 dd offset sub_40210E 21.rdata:004983CC dd offset sub_40229E 22.rdata:004983D0 dd offset sub_4022EE 23.rdata:004983D4 dd offset sub_40248F 24.rdata:004983D8 dd offset sub_4027D0 25.rdata:004983DC dd offset sub_4028F5 26.rdata:004983E0 dd offset sub_402995 27.rdata:004983E4 dd offset sub_402B25 28.rdata:004983E8 dd offset sub_402B75 29.rdata:004983EC dd offset sub_402D16 30.rdata:004983F0 dd offset sub_403057 31.rdata:004983F4 dd offset sub_40317C 32.rdata:004983F8 dd offset sub_40321C 33.rdata:004983FC dd offset sub_4033AC 34.rdata:00498400 dd offset sub_4033FC 35.rdata:00498404 dd offset sub_40359D 36.rdata:00498408 dd offset sub_4038DE 37.rdata:0049840C dd offset sub_403A03 38.rdata:00498410 dd offset sub_403AA3 39.rdata:00498414 dd offset sub_403CFC 40.rdata:00498418 dd offset sub_403D75 41.rdata:0049841C dd offset sub_403FF8 42.rdata:00498420 dd offset sub_404339 43.rdata:00498424 dd offset sub_40445E 44.rdata:00498428 dd offset sub_4044FE 45.rdata:0049842C dd offset sub_40468E 46.rdata:00498430 dd offset sub_4046DE 47.rdata:00498434 dd offset sub_40487F 48.rdata:00498438 dd offset sub_404BC0 49.rdata:0049843C dd offset sub_404CE5 50.rdata:00498440 dd offset sub_404D85
- Explanation: Each pointer initializes a set of strings/tokens for specific theft categories. This modular setup allows easy updates to target new wallets or browsers.
Encryption/Decryption Routine
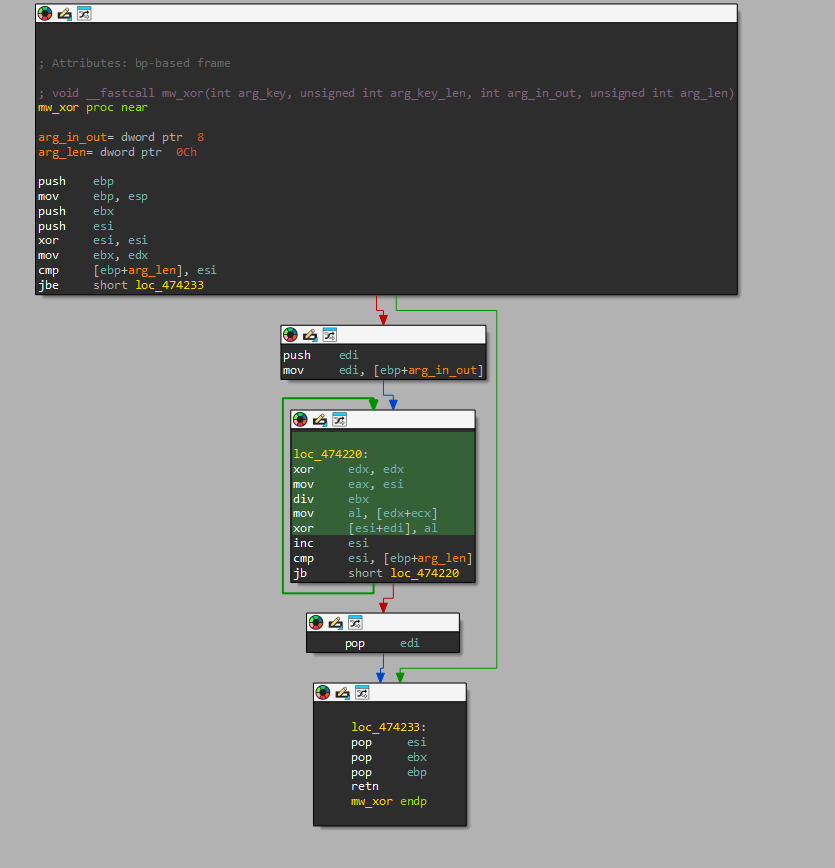
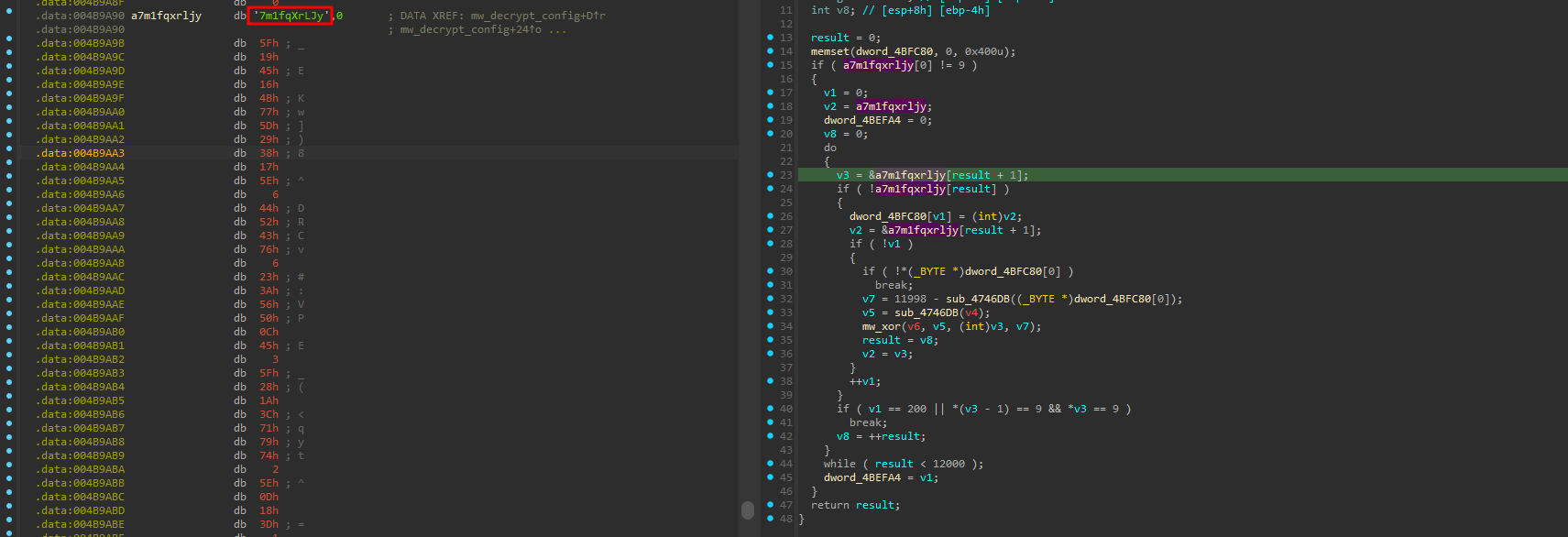
CryptBot uses XOR for string and config decryption. Here's the routine:
c1int sub_417AD2() 2{ 3 int result; // eax 4 int v1; // esi 5 char *v2; // ecx 6 char *v3; // edi 7 _BYTE *v4; // ecx 8 unsigned int v5; // eax 9 int v6; // ecx 10 unsigned int v7; // [esp-8h] [ebp-14h] 11 int v8; // [esp+8h] [ebp-4h] 12 13 result = 0; 14 memset(dword_4BFC80, 0, 0x400u); 15 if ( a7m1fqxrljy[0] != 9 ) 16 { 17 v1 = 0; 18 v2 = a7m1fqxrljy; 19 dword_4BEFA4 = 0; 20 v8 = 0; 21 do 22 { 23 v3 = &a7m1fqxrljy[result + 1]; 24 if ( !a7m1fqxrljy[result] ) 25 { 26 dword_4BFC80[v1] = (int)v2; 27 v2 = &a7m1fqxrljy[result + 1]; 28 if ( !v1 ) 29 { 30 if ( !*(_BYTE *)dword_4BFC80[0] ) 31 break; 32 v7 = 11998 - sub_4746DB((_BYTE *)dword_4BFC80[0]); 33 v5 = sub_4746DB(v4); 34 sub_47420E(v6, v5, (int)v3, v7); 35 result = v8; 36 v2 = v3; 37 } 38 ++v1; 39 } 40 if ( v1 == 200 || *(v3 - 1) == 9 && *v3 == 9 ) 41 break; 42 v8 = ++result; 43 } 44 while ( result < 12000 ); 45 dword_4BEFA4 = v1; 46 } 47 return result; 48}
The core XOR function (sub_47420E):
c1void __fastcall sub_47420E(int a1, unsigned int a2, int a3, unsigned int a4) 2{ 3 unsigned int i; // esi 4 5 for ( i = 0; i < a4; ++i ) 6 *(_BYTE *)(i + a3) ^= *(_BYTE *)(i % a2 + a1); 7}
- Renamed for Clarity:
c1void __fastcall mw_xor(int arg_key, unsigned int arg_key_len, int arg_in_out, unsigned int arg_len) 2{ 3 unsigned int i; // esi 4 5 for ( i = 0; i < arg_len; ++i ) 6 *(_BYTE *)(i + arg_in_out) ^= *(_BYTE *)(i % arg_key_len + arg_key); 7}
- Explanation: This is a simple rolling XOR using a key like
7m1fqXrLJy. It decrypts config data, including C2 URLs.
IDA view of the XOR routine:
Config Decryption Example
The key 7m1fqXrLJy is hardcoded.
Using CyberChef or similar tools:
- Extract encrypted data as hex (e.g.,
5F1945164B775D2938175E064452437606233A56500C45035F281A3C717974025E0D183D). - Convert to UTF-8.
- XOR with key
7m1fqXrLJy.
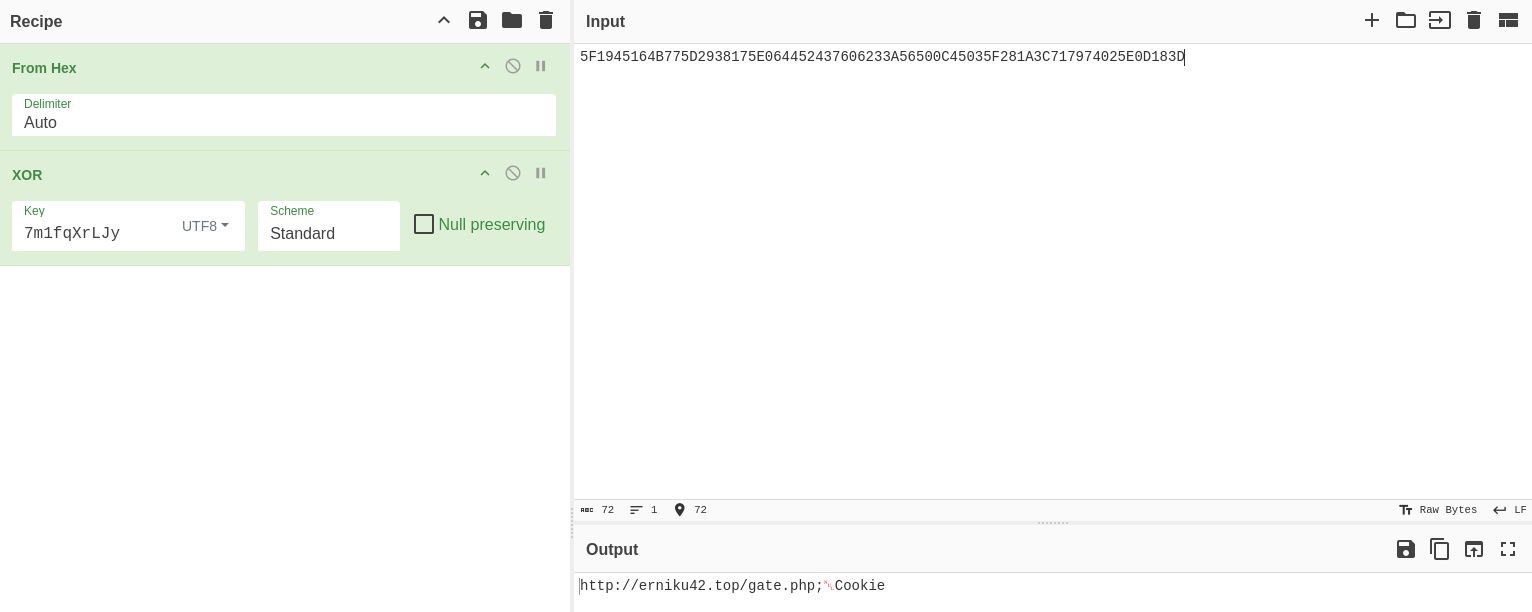
Result: Decrypted config like http://erniku42.top/gate.php;.Cookie.
Signature for key check:
nasm1B9 00 01 00 00 mov ecx, 100h 280 3D ?? ?? ?? ?? 09 cmp byte ptr a7m1fqxrljy, 9 ; "7m1fqXrLJy"
Note: Keys vary across samples; ?? represents placeholders.
Malware Configuration Extractor
This Python script extracts the encrypted config using PE parsing and XOR decryption. It's self-contained and works on unpacked samples.
python1# CryptBot Configuration Extractor 2# This script extracts the encrypted configuration from an unpacked CryptBot malware sample. 3# It locates the XOR key and encrypted config data in the .text section of a PE file, 4# decrypts the config using the identified key, and outputs the C2 address and settings. 5# Dependencies: pefile, re, struct 6# Usage: Replace '/tmp/cryptbot.bin' with the path to your malware sample. 7# Output: A dictionary containing the C2 URL and key-value settings. 8 9import re 10import pefile 11import struct 12 13file_data = open('/tmp/cryptbot.bin', 'rb').read() 14pe = pefile.PE(data = file_data) 15image_base = pe.OPTIONAL_HEADER.ImageBase 16 17text_data = None 18 19for s in pe.sections: 20 if b'.text' == s.Name[:5]: 21 text_data = s.get_data() 22 break 23 24assert text_data is not None 25 26# Regular expressions to match XOR key check instructions 27# These patterns look for specific assembly instructions that reference the XOR key 28eggs = [ 29 rb'\x80\x3D(....)\x09\xB9\x00\x01\x00\x00', 30 rb'\xB9\x00\x01\x00\x00\x80\x3D(....)\x09' 31 ] 32 33candidate_offsets = [] 34 35for egg in eggs: 36 for m in re.finditer(egg, text_data, re.DOTALL): 37 try: 38 candidate_va = struct.unpack('<I', m.group(1))[0] 39 candidate_offset = pe.get_offset_from_rva(candidate_va - image_base) 40 candidate_offsets.append(candidate_offset) 41 42 except: 43 print(f"failed for group {m.group(1)}!") 44 pass 45 46assert len(candidate_offsets) != 0 47 48def xor_decrypt(data, key): 49 out = [] 50 for i in range(len(data)): 51 out.append(data[i] ^ key[i % len(key)]) 52 return bytes(out) 53 54 55def get_config(data, offset): 56 key = data[offset:].split(b'\x00')[0] 57 assert 5 < len(key) < 20 58 config_data_enc = data[offset + len(key) + 1:] 59 return xor_decrypt(config_data_enc, key) 60 61config_data = None 62 63for candidate_offset in candidate_offsets: 64 try: 65 tmp_config = get_config(file_data, candidate_offset) 66 if tmp_config[:4] == b'http': 67 config_data = tmp_config 68 break 69 except: 70 pass 71 72assert config_data is not None 73 74config_array = [] 75for a in config_data.split(b'\x00'): 76 if not a.isascii(): 77 break 78 config_array.append(a) 79 80c2 = config_array[0] 81settings = [] 82 83for config_entries in config_array[1:]: 84 for entry in config_entries.split(b'<>\r\n'): 85 if len(entry) == 0: 86 continue 87 settings.append({'key': entry.split(b'<>_<>')[0].decode('utf-8'),'value':entry.split(b'<>_<>')[1].decode('utf-8')}) 88 89assert len(settings) != 0 90 91final_config = {'C2':c2, 'Settings':settings} 92 93print(final_config)
- Usage: Replace
/tmp/cryptbot.binwith your sample path. Outputs C2 and settings dictionary. - Explanation: Searches for key signature, extracts and decrypts config. Handles variations in packing.
Running the script on a sample will yield the C2 address and configuration settings used by the malware as the following output:
json1{ 2 "C2":"b""http://erniku42.top/gate.php;", 3 "Settings":[ 4 { 5 "key":"CookiesEdge", 6 "value":"false" 7 }, 8 { 9 "key":"HistoryEdge", 10 "value":"false" 11 }, 12 { 13 "key":"HistoryFirefox", 14 "value":"false" 15 }, 16 { 17 "key":"EdgeDB", 18 "value":"true" 19 }, 20 { 21 "key":"Edge", 22 "value":"false" 23 }, 24 { 25 "key":"Files", 26 "value":"false" 27 }, 28 { 29 "key":"Opera", 30 "value":"false" 31 }, 32 { 33 "key":"CookiesOpera", 34 "value":"false" 35 }, 36 { 37 "key":"HistoryOpera", 38 "value":"false" 39 }, 40 { 41 "key":"Screenshot", 42 "value":"true" 43 }, 44 { 45 "key":"Chrome", 46 "value":"false" 47 }, 48 { 49 "key":"Info", 50 "value":"true" 51 }, 52 { 53 "key":"HistoryChrome", 54 "value":"false" 55 }, 56 { 57 "key":"ChromeDB", 58 "value":"true" 59 }, 60 { 61 "key":"Wallet", 62 "value":"true" 63 }, 64 { 65 "key":"ChromeExt", 66 "value":"true" 67 }, 68 { 69 "key":"Firefox", 70 "value":"false" 71 }, 72 { 73 "key":"CookiesChrome", 74 "value":"false" 75 }, 76 { 77 "key":"FirefoxDB", 78 "value":"true" 79 }, 80 { 81 "key":"CookiesFirefox", 82 "value":"false" 83 }, 84 { 85 "key":"Desktop", 86 "value":"true" 87 }, 88 { 89 "key":"EdgeExt", 90 "value":"true" 91 }, 92 { 93 "key":"CookiesFile", 94 "value":"_AllCookies.txt" 95 }, 96 { 97 "key":"HistoryFile", 98 "value":"_AllHistory.txt" 99 }, 100 { 101 "key":"NTFS", 102 "value":"true" 103 }, 104 { 105 "key":"Key", 106 "value":"NkB7vazOVtAR2LZ" 107 }, 108 { 109 "key":"DesktopFolder", 110 "value":"_Desktop" 111 }, 112 { 113 "key":"UAC", 114 "value":"false" 115 }, 116 { 117 "key":"ScreenFile", 118 "value":"$CREEN.PNG" 119 }, 120 { 121 "key":"DeleteAfterEnd", 122 "value":"true" 123 }, 124 { 125 "key":"MessageAfterEnd", 126 "value":"false" 127 }, 128 { 129 "key":"FirefoxDBFolder", 130 "value":"_Firefox" 131 }, 132 { 133 "key":"Anti", 134 "value":"false" 135 }, 136 { 137 "key":"EdgeDBFolder", 138 "value":"_Edge" 139 }, 140 { 141 "key":"UserAgent", 142 "value":"" 143 }, 144 { 145 "key":"Prefix", 146 "value":"mrd-" 147 }, 148 { 149 "key":"WalletFolder", 150 "value":"_Wallet" 151 }, 152 { 153 "key":"PasswordFile", 154 "value":"_AllPasswords.txt" 155 }, 156 { 157 "key":"ChromeDBFolder", 158 "value":"_Chrome" 159 }, 160 { 161 "key":"ExternalDownload", 162 "value":"http://ovapfa05.top/unfele.dat" 163 }, 164 { 165 "key":"FilesFolder", 166 "value":"_Files" 167 }, 168 { 169 "key":"InfoFile", 170 "value":"_Information.txt" 171 } 172 ] 173}
Impersonation
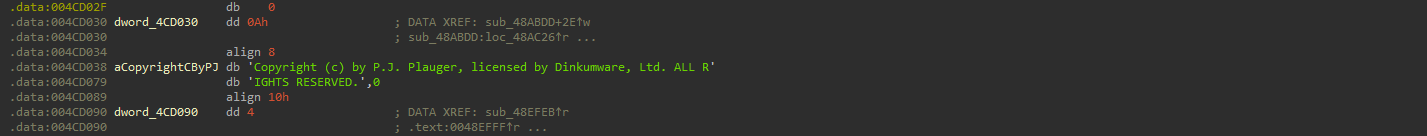
An interesting finding: CryptBot impersonates legitimate software from "Dinkumware Ltd" (a C++ library provider) to blend in.
After running YARA (see below), another sample was hit: eeded5f5d006dacd9e2f33ba9fad47332c04b57f621c89731376f51127198345.
YARA Rule
This refined YARA rule detects CryptBot based on characteristic strings for system info collection. It includes more specificity and metadata.
c1rule CryptBot { 2 meta: 3 description = "Detects CryptBot infostealer based on characteristic strings in its configuration or output" 4 triage_description = "Identifies CryptBot malware by matching strings related to system information collection, such as UID, UserName, ComputerName, and admin status" 5 triage_score = 8 6 author = "0xw43l" 7 date = "2025-08-15" 8 reference = "https://any.run/cybersecurity-blog/cryptbot-infostealer-malware-analysis/" 9 hash = "7ccda59528c0151bc9f11b7f25f8291d99bcf541488c009ef14e2a104e6f0c5d" 10 strings: 11 $s1 = "UID:" ascii wide 12 $s2 = "UserName:" ascii wide 13 $s3 = "ComputerName:" ascii wide 14 $s4 = "DateTime:" ascii wide 15 $s5 = "UserAgent:" ascii wide 16 $s6 = "Keyboard Languages:" ascii wide 17 $s7 = "Display Resolution:" ascii wide 18 $s8 = "CPU:" ascii wide 19 $s9 = "RAM:" ascii wide 20 $s10 = "GPU:" ascii wide 21 $s11 = "isGodMod: yes" ascii wide 22 $s12 = "isGodMod: no" ascii wide 23 $s13 = "isAdmin: yes" ascii wide 24 $s14 = "isAdmin: no" ascii wide 25 $s15 = "Installed software:" ascii wide 26 $xor_key = "7m1fqXrLJy" ascii // Common XOR key 27 condition: 28 uint16(0) == 0x5A4D and // PE header 29 all of ($s*) or 30 ($xor_key and 10 of ($s*)) 31}
MITRE ATT&CK
CryptBot aligns with several MITRE ATT&CK techniques. Below is a mapping based on observed behaviors:
| Tactic | Technique ID | Technique Name | Description | |---------------------|--------------|-----------------------------------------|-------------| | Initial Access | T1189 | Drive-by Compromise | Distributed via malvertising or fake software downloads. | | Execution | T1204 | User Execution: Malicious File | Users execute cracked software bundles. | | Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys | Adds registry entries for persistence. | | Privilege Escalation | T1068 | Exploitation for Privilege Escalation | Checks for admin/God Mode and escalates if possible. | | Defense Evasion| T1027 | Obfuscated Files or Information | Uses XOR encryption for strings and config. | | Credential Access | T1555 | Credentials from Password Stores | Steals browser passwords and cookies. | | Discovery | T1082 | System Information Discovery | Collects UID, CPU, RAM, GPU, etc. | | Collection | T1113 | Screen Capture | Takes screenshots. | | Collection | T1056.001 | Input Capture: Keylogging | Captures keystrokes. | | Exfiltration | T1041 | Exfiltration Over C2 Channel | Sends data to C2 via HTTP. |
- Sources: Based on analyses from ANY.RUN, AhnLab, and MITRE mappings for infostealers. For full matrix, see MITRE ATT&CK Navigator.
IOCs
The following table consolidates Indicators of Compromise (IOCs) related to CryptBot, PrivateLoader, SmokeLoader, Amadey, Lumma, Stealc, and Redline malware, including file hashes, domains, IP addresses, ASNs, and specific URLs used for command-and-control (C2) or payload delivery. These IOCs can be used for detection, threat hunting, and mitigation in security operations.
| Value | Type | Description | |---------------------------------------------------------------------------|------------|---------------------------------------------------| | da7fadc671804e093c7dcad3455a266e77d2c84b641ae037c70004daaa05b897 | SHA-256 | CryptBot – “Channel4.exe” | | 8874ee4d9c878a6dc7f2681ec36df05cb09c44ccb3be0ec89569f5bdece80519 | SHA-256 | CryptBot – “66dd5fafdeab3_lyla.exe” | | 2a5dd73271b9eabe63e7aefc5dc2ec01921ffba8bfa7ee278a2180e597c97bf7 | SHA-256 | CryptBot – “Set-up.exe” | | 319d1dc217b7e83a85dd62cb2c066156ba5579087f11c991a99089606979ca28 | SHA-256 | PrivateLoader payload | | 7631726b15a0cba30f88268df626df7a053c044efc78f772ade21e879cc7ae58 | SHA-256 | SmokeLoader payload | | 7b41cabcafca0e5725c874d316f4f5f83561fa571240c0ccdd8b19034282bf41 | SHA-256 | Amadey payload | | dfdc63994c85f7161e25a26b762835781ce5578c6a5b5c2839324fc7faa591d3 | SHA-256 | Stage2 CryptBot payload DLL | | dfefcc62121ee76f84d382fc622b61321f149a04a848c8cb987a7bda7ca59941 | SHA-256 | Stage2 CryptBot payload DLL | | tventyv20sb[.]top | Domain | CryptBot C2 | | twoxv2sr[.]top | Domain | CryptBot C2 | | analforeverlovyu[.]top | Domain | CryptBot C2 | | thirtv13pn[.]top | Domain | CryptBot C2 | | bdtwo2sb[.]top | Domain | CryptBot C2 | | neiz19ht[.]top | Domain | CryptBot C2 | | levz11ht[.]top | Domain | CryptBot C2 | | fifxv15pn[.]top | Domain | CryptBot C2 | | fivevd5ht[.]top | Domain | CryptBot C2 | | sevtvd17ht[.]top | Domain | CryptBot C2 | | rxeight8ht[.]top | Domain | CryptBot C2 | | salvatiiywo[.]shop | Domain | Lumma C2 | | ignoracndwko[.]shop | Domain | Lumma C2 | | preachstrwnwjw[.]shop | Domain | Lumma C2 | | complainnykso[.]shop | Domain | Lumma C2 | | basedsymsotp[.]shop | Domain | Lumma C2 | | charistmatwio[.]shop | Domain | Lumma C2 | | grassemenwji[.]shop | Domain | Lumma C2 | | stitchmiscpaew[.]shop | Domain | Lumma C2 | | commisionipwn[.]shop | Domain | Lumma C2 | | epohe[.]ru | Domain | SmokeLoader C2 | | olihonols.in[.]net | Domain | SmokeLoader C2 | | nicetolosv[.]xyz | Domain | SmokeLoader C2 | | jftolsa[.]ws | Domain | SmokeLoader C2 | | download-rarfree[.]com | Domain | Redirecting to CryptBot payloads | | rar-uploader[.]com | Domain | Redirecting to CryptBot payloads | | economartbd[.]com | Domain | Redirecting to CryptBot payloads | | rarz-uploader[.]com | Domain | Redirecting to CryptBot payloads | | adsbell[.]com | Domain | Redirecting to CryptBot payloads | | voiceofchangeinternational[.]com | Domain | Redirecting to CryptBot payloads | | rar-freeload[.]com | Domain | Redirecting to CryptBot payloads | | rars-freeload[.]com | Domain | Redirecting to CryptBot payloads | | download-rarsfree[.]com | Domain | Redirecting to CryptBot payloads | | rarzload-official[.]com | Domain | Redirecting to CryptBot payloads | | Chuanpupu[.]com | Domain | Redirecting to CryptBot payloads | | techjbc[.]xyz | Domain | Redirecting to CryptBot payloads | | papiblendz[.]com | Domain | Redirecting to CryptBot payloads | | sarahmakesitbetter[.]com | Domain | Redirecting to CryptBot payloads | | rivistablog[.]com | Domain | Redirecting to CryptBot payloads | | anotherconversation[.]com | Domain | Redirecting to CryptBot payloads | | super6-star[.]buzz | Domain | Redirecting to CryptBot payloads | | bluelineagenciamentodecargas[.]com | Domain | Redirecting to CryptBot payloads | | peace-motion[.]buzz | Domain | Redirecting to CryptBot payloads | | 131ldvip[.]com | Domain | Redirecting to CryptBot payloads | | onlineofficetutorials[.]com | Domain | Redirecting to CryptBot payloads | | puntext[.]com | Domain | Redirecting to CryptBot payloads | | free4pc[.]shop | Domain | Redirecting to CryptBot payloads | | allgetintopcc[.]cfd | Domain | Redirecting to CryptBot payloads | | techjbc[.]cfd | Domain | Redirecting to CryptBot payloads | | sultanisback[.]pro | Domain | Redirecting to CryptBot payloads | | filemirrormegaz[.]shop | Domain | Redirecting to CryptBot payloads | | uznhmij5kr2307244[.]click | Domain | Redirecting to CryptBot payloads | | afrdrctf[.]com | Domain | Redirecting to CryptBot payloads | | up4pc[.]com | Domain | Offering fake cracked software | | driver-booster-key[.]com | Domain | Offering fake cracked software | | securecracked[.]info | Domain | Offering fake cracked software | | filecrr[.]org | Domain | Offering fake cracked software | | soft98[.]org | Domain | Offering fake cracked software | | haxpc[.]net | Domain | Offering fake cracked software | | muzamilpc[.]com | Domain | Offering fake cracked software | | alphasofts[.]net | Domain | Offering fake cracked software | | preactivated[.]net | Domain | Offering fake cracked software | | mycrackfree[.]com | Domain | Offering fake cracked software | | drapk[.]net | Domain | Offering fake cracked software | | rgames31[.]com | Domain | Offering fake cracked software | | windows-7-activator[.]com | Domain | Offering fake cracked software | | modcrack[.]net | Domain | Offering fake cracked software | | office-activator[.]com | Domain | Offering fake cracked software | | official-kmspico[.]com | Domain | Offering fake cracked software | | kmspico[.]ws | Domain | Offering fake cracked software | | kmspicoofficial[.]com | Domain | Offering fake cracked software | | windows4pc[.]com | Domain | Offering fake cracked software | | windowsprodcutkey[.]com | Domain | Offering fake cracked software | | activationkeysfree[.]org | Domain | Offering fake cracked software | | serialhax[.]org | Domain | Offering fake cracked software | | bcrack[.]org | Domain | Offering fake cracked software | | crack4tech[.]org | Domain | Offering fake cracked software | | crackedaxe[.]com | Domain | Offering fake cracked software | | crackingcity[.]org | Domain | Offering fake cracked software | | crackspc[.]net | Domain | Offering fake cracked software | | fileserialkey[.]net | Domain | Offering fake cracked software | | fullycracksoft[.]com | Domain | Offering fake cracked software | | ifree4pc[.]net | Domain | Offering fake cracked software | | productkeysfree[.]org | Domain | Offering fake cracked software | | tech4pc[.]org | Domain | Offering fake cracked software | | winows4pc[.]com | Domain | Offering fake cracked software | | 4mirrorpc[.]net | Domain | Offering fake cracked software | | drfiles[.]net | Domain | Offering fake cracked software | | haxacademy[.]net | Domain | Offering fake cracked software | | crackfullpc[.]org | Domain | Offering fake cracked software | | crackmacs[.]org | Domain | Offering fake cracked software | | crackmarkets[.]com | Domain | Offering fake cracked software | | pesktop[.]org | Domain | Offering fake cracked software | | crackpcsoft[.]org | Domain | Offering fake cracked software | | crackdownloads[.]org | Domain | Offering fake cracked software | | iup4pc[.]net | Domain | Offering fake cracked software | | crackingpc[.]net | Domain | Offering fake cracked software | | downloadvst[.]com | Domain | Offering fake cracked software | | licensedfull[.]com | Domain | Offering fake cracked software | | vstcrackpc[.]com | Domain | Offering fake cracked software | | vstpropc[.]com | Domain | Offering fake cracked software | | vstdownload[.]org | Domain | Offering fake cracked software | | activationskey[.]com | Domain | Offering fake cracked software | | allmacworld[.]net | Domain | Offering fake cracked software | | cracked-minecraft[.]com | Domain | Offering fake cracked software | | crackedvpn[.]com | Domain | Offering fake cracked software | | crackfix[.]net | Domain | Offering fake cracked software | | crackfullkeys[.]com | Domain | Offering fake cracked software | | crackfullpc[.]net | Domain | Offering fake cracked software | | cracksecure[.]com | Domain | Offering fake cracked software | | cracksoftpro[.]com | Domain | Offering fake cracked software | | crackswatch[.]com | Domain | Offering fake cracked software | | crackvstpc[.]com | Domain | Offering fake cracked software | | downloadworld[.]org | Domain | Offering fake cracked software | | fullidmcrack[.]com | Domain | Offering fake cracked software | | fullproductkeys[.]com | Domain | Offering fake cracked software | | idmfreedownload[.]net | Domain | Offering fake cracked software | | idmfullcrack[.]info | Domain | Offering fake cracked software | | idmpatchdownload[.]com | Domain | Offering fake cracked software | | idmpatched[.]com | Domain | Offering fake cracked software | | idmpc[.]co | Domain | Offering fake cracked software | | igetintopc[.]com[.]pk | Domain | Offering fake cracked software | | kanjupc[.]com | Domain | Offering fake cracked software | | keyproductkey[.]com | Domain | Offering fake cracked software | | licensekey[.]cc | Domain | Offering fake cracked software | | macsoftkey[.]com | Domain | Offering fake cracked software | | naveedcrack[.]com | Domain | Offering fake cracked software | | office4pc[.]com | Domain | Offering fake cracked software | | pc4download[.]com | Domain | Offering fake cracked software | | pcbank[.]org | Domain | Offering fake cracked software | | pccrack[.]org | Domain | Offering fake cracked software | | pcdrives[.]org | Domain | Offering fake cracked software | | pcexe[.]net | Domain | Offering fake cracked software | | pcsoftcrack[.]net | Domain | Offering fake cracked software | | pdffree[.]net | Domain | Offering fake cracked software | | pluginstorrent[.]net | Domain | Offering fake cracked software | | premiumpc[.]net | Domain | Offering fake cracked software | | premiumpc[.]org | Domain | Offering fake cracked software | | procracked[.]org | Domain | Offering fake cracked software | | procrackwin[.]com | Domain | Offering fake cracked software | | productkeycrack[.]com | Domain | Offering fake cracked software | | productkeyspc[.]com | Domain | Offering fake cracked software | | productskey[.]org | Domain | Offering fake cracked software | | prolicensefree[.]com | Domain | Offering fake cracked software | | proserialcrack[.]com | Domain | Offering fake cracked software | | proserialfree[.]com | Domain | Offering fake cracked software | | provstpc[.]com | Domain | Offering fake cracked software | | pubgcrack[.]net | Domain | Offering fake cracked software | | rootcracks[.]com | Domain | Offering fake cracked software | | sadeempc[.]info | Domain | Offering fake cracked software | | securecracked[.]info | Domain | Offering fake cracked software | | seriakkeyforfree[.]com | Domain | Offering fake cracked software | | softsmac[.]net | Domain | Offering fake cracked software | | softwarein1[.]com | Domain | Offering fake cracked software | | softwarekeep[.]info | Domain | Offering fake cracked software | | starcracked[.]net | Domain | Offering fake cracked software | | startcrack[.]info | Domain | Offering fake cracked software | | topfullcrack[.]com | Domain | Offering fake cracked software | | topfullkeys[.]com | Domain | Offering fake cracked software | | torrent4pc[.]com | Domain | Offering fake cracked software | | torrentpc[.]org | Domain | Offering fake cracked software | | vst4cracked[.]com | Domain | Offering fake cracked software | | vst4pc[.]com | Domain | Offering fake cracked software | | vstfree[.]org | Domain | Offering fake cracked software | | vstfreedownload[.]com | Domain | Offering fake cracked software | | vstfullpc[.]com | Domain | Offering fake cracked software | | vstpc[.]com | Domain | Offering fake cracked software | | vstpluginsdownload[.]org | Domain | Offering fake cracked software | | vstzip[.]com | Domain | Offering fake cracked software | | wincrackbox[.]com | Domain | Offering fake cracked software | | soft-got[.]org | Domain | Offering fake cracked software | | 185.244.181[.]38 | IPv4 | CryptBot C2 | | 81.94.159[.]120 | IPv4 | CryptBot C2 | | 103.130.147[.]211 | IPv4 | Hosting malwares | | 147.45.44[.]104 | IPv4 | Hosting malwares - Operated by PrivateLoader | | 31.41.244[.]9 | IPv4 | Hosting malwares - Operated by PrivateLoader | | 176.111.174[.]109 | IPv4 | Hosting malwares - Operated by PrivateLoader | | 147.45.47[.]169 | IPv4 | PrivateLoader C2 | | 212.113.116[.]202 | IPv4 | PrivateLoader C2 | | 62.133.61[.]172 | IPv4 | PrivateLoader C2 | | 45.91.200[.]135 | IPv4 | PrivateLoader C2 | | 92.246.139[.]82 | IPv4 | PrivateLoader C2 | | 185.215.113[.]16 | IPv4 | Amadey C2 | | 185.215.113[.]19 | IPv4 | Amadey C2 | | 185.215.113[.]17 | IPv4 | Stealc C2 | | 91.202.233[.]158 | IPv4 | Stealc C2 | | 185.215.113[.]67 | IPv4 | Redline C2 | | 65.21.18[.]51 | IPv4 | Redline C2 | | 215789 | ASN | “Karina Rashkoska” | | 214927 | ASN | “PSB HOSTING LTD” | | 210644 | ASN | “Aeza International Ltd” | | 216246 | ASN | “Aeza Group Ltd.” | | 51381 | ASN | “1337TEAM LIMITED” | | 60424 | ASN | “1337TEAM LIMITED” | | 56873 | ASN | “1337TEAM LIMITED” | | 39770 | ASN | “1337TEAM LIMITED” | | 200593 | ASN | “PROSPERO OOO” |
URLs
The following URLs are associated with CryptBot C2 or payload delivery:
- http://home.eightji8ht.top/KTGbGvOSGlkPaQeuKdDL1572982449
- http://home.eightjo8sr.top/aCrmSMJLJEOsinOjzktg1889307302
- http://home.eightjo8vt.top/APWuDeoyrwjlLWFqpzlR1427917304
- http://home.eightjo8vt.top/GZAiWBsUWZXSjptiVgki1273022183
- http://home.eightjp8ht.top/FlchnxzGeSIHRPHPeYBm1318897305
- http://home.eightjp8vs.top/GyoNxLolJLOIDEEeLXwl1239497306
- http://home.eightjp8vs.top/feCIlgpoToBMdGHZfMGS1673054910
- http://home.eleja11sb.top/sSWxMfiKsjZhqgwqlqVX1737823123
- http://home.elevji11ht.top/XmQBHJYvyxRHnDxzxNoj124497298
- http://home.fiveji5ht.top/KlekgDAXLoeekVhmYBHz1732002979
- http://home.fiveji5ht.top/daxtYswdSfyAXDsFwHuK1726572986
- http://home.fiveji5ht.top/sYxNRoYrKJVZJBDMKRQb1729750322
- http://home.fiveji5vs.top/nGdZCFwukcqnsrEfVnqT1732922995
- http://home.fiveji5vt.top/NEpdjvSGIHCSlQWulCHt1776642968
- http://home.fivejo5sr.top/JNzvTWFWHwIXwNBdDJiw1743043030
- http://home.fivejo5sr.top/bTMlLHJsULflKiuhSKNo1745983026
- http://home.fivejo5vt.top/WTAjeFpNiEIhCJndAXAf1714163020
- http://home.fivejo5vt.top/bLeFEuIyIOOFgvRzlwsw1730462437
- http://home.fivejo5vt.top/jQDBoCTTJMoxHduEQtVi1718333022
- http://home.fivejo5vt.top/zViguzTHOAJchzMFSLOa1730123672
- http://home.fivejp5vs.top/WMIfiIbwGZlEzunsPmAm1791043054
- http://home.fivejp5vs.top/gEHGWhRNbwRFXwunSKCi1794913063
- http://home.fivjp5vt.top/GpXJRdeQulqmvESjfFlL1730790181
- http://home.fivjp5vt.top/MzxdLTzahBhrwcHfikEE1730826262
- http://home.forjh4ht.top/wGcuvRVzmafViJJtVGWe1729706625
- http://home.forji14vs.top/SRmkbXbtICjnsFSsyIIU1719933008
- http://home.forji14vs.top/vLzEmBxYDkDWwAHlJbwm1756532992
- http://home.forjo14vt.top/vZEhEBivXldclXHuMstz1714163020
- http://home.forpz4ht.top/cQOBChluQKBYyXAKOlUj1729771262
- http://home.neinja9ht.top/LQEGldMWvlStBQQIEVyV1797523097
- http://home.neinja9ht.top/xplvzowOfiYMuqANrGoq1730957812
- http://home.neinjo9vt.top/TCEdaQJXYbawpvRtmzAl1724603017
- http://home.neinjo9vt.top/fcOoKJiqkEdEfaSKlDpf1730221830
- http://home.neinjp9sr.top/VQZWuwklsiAqwKSHENhk1730865247
- http://home.ninjo19vs.top/kbrGrXsSXkmNPHYxWled1730607975
- http://home.oneji1vt.top/yYwXoctNQsNlxniaRRXW1729687663
- http://home.onejo1vs.top/VlQbIzlsEdAqLBFZBoYY1734910639
- http://home.onejo1vs.top/rwucRRJvgOJMYBxNQZTH1731060549
- http://home.onejo1vt.top/TgyonuAhQqHmRNCTtLXO1730221831
- http://home.onejo1vt.top/VBkFCJscNZobpQzbgGkx1736750123
- http://home.onejo1vt.top/pgpVedqwyWTKdnDvLton1739150427
- http://home.onejp1ht.top/EydgSnlRvnipiEFgnals1733640997
- http://home.onejp1ht.top/wjfslbMBCTjPKLMdHjMB1739381071
- http://home.onejp1vt.top/WVWXLEBFUCjXpjDFcYnq1730826262
- http://home.sevja17sb.top/LMiwiyYekyuSDTCvLbPv1765833112
- http://home.sevja17sb.top/ZsSuJntZcwEFCFkTKSrm1784413120
- http://home.sevjoi17ht.top/RZveVhltLlnLSesEiEKb1573051889
- http://home.sevjoi17sr.top/TCQEoezkVqyvrJjqBhZs1204307303
- http://home.sevjoi17vt.top/FhmmyqGhAphHaXwiJfvm1273042791
- http://home.sevjoi17vt.top/cZQSdrLXfSobDdFnqveX1701417302
- http://home.sevjp17vt.top/UDnaUWBbCguivjcJTAFI1730790183
- http://home.sevtji17vt.top/AtMFEEDPmrFgjjlYWVjB1487667296
- http://home.sivji6ht.top/nQOeaKPXEODJmfbxNDgw1726939767
- http://home.sivjo6vt.top/NkVbPqNMrXCEggsfRWGb1734600172
- http://home.sivjo6vt.top/RLcrqDvFJmGzdgZTXBGX1734380462
- http://home.sivjo6vt.top/ltLNFctqJMohaGeCvuMv1738320221
- http://home.sivjp6ht.top/lBxeEWboCtkXsZBdYMeP1738950518
- http://home.sixjp6sr.top/jtrLzFxhLfniIyrmfEOG1737810904
- http://home.sixtlm16ht.top/nbGcgYkZqJUuAbjyAxww1567697297
- http://home.sixtlm16sr.top/TGHTqHPiFFfksEXbQHwc1509887296
- http://home.tenja10ht.top/IGVMsWdjbQifeqDGdLik1778133095
- http://home.tenji10ht.top/MVPXmuUIFAQLfQdTpqGi1776942976
- http://home.tenjo10ht.top/FXpkGDyUTRqQxEvMSiPD1764033034
- http://home.tenjo10vt.top/paKURpJFxJCnukXyqZrN1779133042
- http://home.tenjp10vs.top/SFyYktVKDQBaqLympWfA1794923063
- http://home.thirtji13ht.top/MwOBqdodAGbyXMofAyrU5986261729
- http://home.thirtjo13sr.top/bYcMGmpHJcbGkomonWsU0126461730
- http://home.thirtjo13vt.top/FMmMtBkQtjnpYGvmAcfX3322181730
- http://home.thirtjo13vt.top/rvAMJqturkAmDaZoTnSo7412361730
- http://home.thirtjo13vt.top/xaDSPDgkqKmDlPNoQLbs1617302014
- http://home.tventji20ht.top/axNhXgnGYoPSgajZFkaQ5917298626
- http://home.tventji20vs.top/NWYJPzCYEvZpxoyKvBIK9295321729
- http://home.tventjo20sr.top/pLDNcrnQYnSceQqdUDvf0117302646
- http://home.tventjo20vs.top/SOMOJyZWYBxdybbmZeaW1270101730
- http://home.tventjo20vs.top/lwRwtEGztSQcWvXoArFS9063941730
- http://home.tventjo20vt.top/FjnNAcVhtuMKyKxfgwGc3022181730
- http://home.tventjo20vt.top/fExmNYmMwsMkeOPpBLzG1620141730
- http://home.tventjo20vt.top/ztcbHfsrgDVbKwvjMmcq7417301236
- http://home.tventjp20vt.top/julfUeXzXwHcgsxxhkmr6282621730
- http://home.twelja12sb.top/JLEncoVUzpBxNKNLrTYV1908437312
- http://home.twelja12sb.top/xKCOYZtRPmSqQvpgghZS1526587311
- http://home.twelji12ht.top/OsLGYXbzmZdjCMhTnuGb1972979319
- http://home.twelji12ht.top/VqfNYMmqQHyFNagmJCit1767697297
- http://home.twelji12ht.top/wUjNbZBIqtyGhfPTmpke1862657298
- http://home.twelji12vs.top/YKVZcYkIJkgPraRfOHBr1173008199
- http://home.twelji12vs.top/flyGQWUPyIQmXYOpcFMz1866977299
- http://home.twelji12vs.top/nXZUoCnprUWelKqFYScP1053297299
- http://home.tweljo12ht.top/SHfUuTYBULkoesjZJfWj1573051889
- http://home.tweljo12sr.top/AoVYhzVxzHmClkVkBHzK1964597302
- http://home.tweljo12sr.top/GDHlEMZKhUWZBxtHkRwh1573028930
- http://home.tweljo12sr.top/UPMCpUyoKEyLghAHklgZ1473030430
- http://home.tweljo12vs.top/GGjrrjEDEWQrYYIQCiSz1549107305
- http://home.tweljo12vs.top/awDRkLatDdHoLFjLkaTk1173065362
- http://home.tweljo12vt.top/GEZFdXtInPnroqnCxvvX1223677301
- http://home.tweljo12vt.top/OSVrAwHTMqXZwPLPhTMW1773013581
- http://home.tweljo12vt.top/UrZpabYUoOYCIETTggQp1273022183
- http://home.tweljp12ht.top/HoQpbeizPhmxJmnjugER1397367309
- http://home.tweljp12ht.top/QPoNBSMGOKYXiKKSXopP1257817309
- http://home.tweljp12ht.top/gwWsuyjcKfHgnGByabIj1771937310
- http://home.tweljp12ht.top/nQVpoVTlTakzyXMzpriM1279757309
- http://home.tweljp12vt.top/TLkmyWUrcoKSfuQMaKSm1173082626
- http://home.tweljp12vt.top/VszWEchGCZleshrQkPDo1986927307
Sample Files (Downloader SHA-256 Hashes)
The following is a list of downloader samples associated with CryptBot and related malware:
- 001ba21803795a450eac7e26fd14a1ae2ef32a5bad5e30b4dd765aad0e5ce7fe
- 01eff957b996465538f0e6a79791b1e7e551c2cb2d0e5c259bdc4ae3b13f48d6
- 02c7c64a8e5e65f6cd16f32bb9b1a4ac975b7479ffff638a2bb085b13825cab5
- 03e37248166df72e91aeb9640513d5a53ec449da4441af43263b447dbd38408b
- 051084d7828f88b80d0ae27fdd3c4baebba7fc82a916f8e7ce6376daf548cc20
- 08be4b7219442aadc19810463457dbd7bab6699f4de6e4dc00617d3429bd5b8c
- 0ad7e833d526131900916008913dec998360ee6d1a9aacf3997602e1cfc1c3e3
- 0f0c0fd81a7f69e33f27f920d639b4aa79c13a74f49231a756f41c3e94f206ab
- 1038bd204447881ed29e44f2288512d14745ad4a9acb1f9c26fbf388f002f9b8
- 12fa7b47d20f0f21ffeb0981eec1d017f377c9539a4d3ad3fca57897c6f5dfdf
- 14fcb1e15c8aae420a36ca53373b062b388605409cf3823642f217643126f07c
- 15b29945c813d2270d4a690719f319e79cda70c1cec2081cba3f05e80b3a549f
- 166421573e82a6a9ba03c7d10167bdb209fd4197305a719ab78b4c2918d69084
- 175957c7b7548858c963338e402325ae2bb249f7cd08d23c3e373b32a68d3b19
- 18b9b073f44dc79731988397997f8875aaf0025f17f89300ca16205b17c0ea35
- 199c28e2ac8b8cf866190c0733c9c010815b86e1eb842f3a9cfa43a73e05491d
- 1d346dcbb0a210552c6da5b8fe300c872b04b8aab052803baeb9f99d9062ad72
- 1f14b8a84d6052e40f434e310716c6a19b5604e194fb3a220d6f156a0cf4a7ff
- 23e7abfa4bbbaf8a8ff8afe139dd1874c4d1aba4826fc462da718ea2147c8c95
- 25e4f9e539d7e0461c55d4b4fa178c1cbb06760139e360da65648d777f118ca0
- 27b7915bbef99f765bee8aaa35f232a488c63138e7c0941da9a27d0057c92af6
- 2b1f016f12fef7124ea7c9898622e650e53814f2d5ff4d76fa712c3e591f9a7f
- 2bf5e06148f88f0ac9a1a33c9fc5b63b7ce65272fa4a234360600732df185007
- 30999b396ce17abf02b7bfb537222186a87c1554a1b9521bfb39dbee45a30288
- 30f0d55b444e180378dfa467bf13b5067b8faba7bc950b4765bb7dbc44ce3ce4
- 32eefa7f0b2893364c0de189b0c8a509ade84a07a463d6a1802c218f0dbb5817
- 332c1b9ad302388edf687fa6a4d8d5ca59dc609aac9215f8d5d8e659af6c615b
- 340d2dc26004646c86973f257b27d0d79491b652b02cc97f9149538cc2b65691
- 362f40028c50b3f13ea8e3ad2096e94ae325a53306d71263e4468101addf765e
- 3668b6e8b80edd909860784c326609470a1655c029dc797dbdceea92a81c83b2
- 3a378046ce52ea095ce8c5ec6aacabb98d73034fbe208dd298cdc75ad3dcfe8e
- 3accb1c82e64cdfce5d0aacd0093f71727575db426f75b77b6c98869c478ec27
- 465a1cefe61446110cc521d376651a5074fb87295da5fd64bd74fd25cbab669b
- 46c168c3108b54ca7f1495182e64b34b4470e8d383781a83a693ec6e6a7725ff
- 4b53e0fdcd937d34cf27f9938a30b977c1f64b5c954e1dc3225aaf4e7ce908ce
- 4b81371832a31aa1b9a3f4caf3da072dbadc9793dc92d90ba3ea89c8ba7dd17e
- 4cd6901726e36bcb39b33343f44a2facb79cfc8bee33e236ff2f603c01bd21a2
- 4ea653d806dd43b18c85cb0642fdaa92028e04864878c8ecb5c08cbe6eb98d61
- 5059ef43cacdc5bb03eb52112084059b3fa3c9f75179e52a9e8814f3c91e6a7f
- 51032e46bebfd6ed04fcc938f5cde48f26df6a0ec48d2b58d31e748c2d87222f
- 53b55b87c5329665f417c43fa8b44e7054183ab13714fd575f4ec73c1576d8d7
- 5ba2ca4455a95b2260a81b6e857735aa697146720db7d15508b69583feb4587d
- 5ea5c9b7b4b7f23b114533a39414f1eac9e6bfd4c1b87786c3840d1f7b6cdf0d
- 5f8d854a6883175c03086c4dfc5d9c8c797facbff6598b41b837f0945d8f1d1c
- 60003b32e48d426f486a0763229dc589ba64a4ca12adfe061732b3497df0930d
- 6008dc1e6448d5f98981eceeb428f0f8eb5ca5d01315073e7751f6812e64b887
- 606df073790843307f1e2cd1455b947a933def47e8a57b7df62f4a0d5e52a26b
- 61a6d4566575e72452bd3304822330f9d2f72accc4dbba11be4748618101fd63
- 6496ed3876803016bf5fb2018c13d9b4f2a7c44253774ebc7c7c36c0e5df7852
- 65841cfa9f5436f51683d7c359e8f2db9dd66723e6c875c6f5fc67d7b1358689
- 6813d84987f1ac92fb6b5d7a9f8ddf26424f44a55022cf9fc5563362c225d8b8
- 690d584a6a58a1e051ab1c0d3c92a3ebbd756125005be6b9ca31c870e801ce90
- 6a0120bf645d3c65aaadf28db313647e773da4d8be6d440f95e3ef3e020f95ce
- 6cb9ea7e7b8f9642e1effb00c75397dbcfe04291c3c61b1561786e46773f3fc2
- 724f947ba0d0b93369f1df6a55fe722889adff5a6f5922d7ab35389feeed13e6
- 73befffc90b6411e42b25b92b4860c8142c82232ff0fb8c247597d0bc09efdbd
- 75328c047ffd60f0ef0f461e8efd11b33f296b8229b9917846ee0a10679a3108
- 76273d86538a5a5ead5ffdae2fcad8d29ae93d736b1f3df1475da71c6a328c7b
- 7ce85df273257bb57c122c1bdceeebe59c16bd8629eff5ad494fb8c387ed7c8a
- 8003fd73d5681b78365343e95c96bf7289fbb66ad2e22673099f4ab4e947270f
- 80c8797268cb88f5bef1791ccc88b62288763a27528709886e55175b9bd94487
- 8350cb907603e05218052fde1fda489957f768aa49dc6ff122a6471d42101aaf
- 862331ec037b258171f1d9a5ff7ba0dd92cc82fab9c130513e4bab50821184e3
- 8682c6f437d339cb9b438cd76f93766dba9ff7db8e9b6ed5103e52d16e93f51f
- 895d6d80e1b7b5ae2745bd7c7d29c9ad3740a4aea90e3ee5035f60ae91ed7c18
- 8af6d1cf38790da6c8205c4cfa20d43e79aebde03571bd881379d1fbbf13f07b
- 8c209705b91becbc186f2aafd2b8dbdffe1b78f0c765ff4d62e9fd7be52c926a
- 8c81a5f325bacafc6094e8d31881ff27de9ecdbcd1c20d67f1e298be09be2ee7
- 8f9fb0dbcf09f7b0a2838323c55a4cb3ce5ebd29230b9afc65cc6e23eb57d107
- 91c3092bc46c0b23b39d0cc10ddeee1b0008d0a12aed25791ed322ef7bc10792
- 9415e13f69bce584aa0e94ba833d689f892d27960f6b6b353f439e4aee32b1aa
- 983d11c7f6d115e3938ebc92b1ade92ea247c44632b3330af256693c2641cb99
- 9b827d471a9e2bd4249aa1cfb80721b97316334fd5aecbc5e2d4296e1c088a12
- 9c45c5456167f65156faa1313ad8bbaffb8aa375669bf756fe0273580a621494
- 9e8de744db5b8cd794226a4df549804f2dcd0f235d035e89305ca093dc3936c2
- a175dbaa581c7064effea9150163c84d5e6e12f975103c31dc13caeb85b62e47
- a2490d03cf08a0cc48030c915a1d6f17a7f755edf84f825df7ae752a358d8837
- a442c37a225f1417da4e67d87d44eb95cb90198f146f09fc4d2da1f716866866
- a55616e2551ae292c035fdb2ceba08327464394e6ec115c424f0e4340a50634d
- a725a1282151b3d66b12e29c116980c7837ae3829682914cf920e0b4520808e7
- aa7c16c9b06e1bc8012e1865a3fa18dd8f43b56c133649fb7ef25400fecea920
- ac94431fdba78b69ba481a37c56e4d067eb26844b64603e946ac402ef344ba4d
- b4222cd9bfbe897a10395414da0f744e223aba7c3ffeee68f03dbd167835c3cb
- b6e865ee7366584424eee3c120bfa7e510fdd1ddd85bd6e59aef57546be13dbd
- b7439cb886010a0f42601044ff3b1ff2cd11873a6e16b6682cba31e052f5865d
- bc417517a6b5949226151ed2dc3b398051fabe68c7c1b1ad92279e6425761962
- bd309518a3159b042d5f766c6159afbad5b18d8c6058d3a20773899a18314b21
- bdd3db5c703b69a6e146f1475d611468ec92053cc25c1b8bd256a56ae1624eb0
- be232e6678efb17e42750a84a60d69ebe71b0bff28e028a375559499782a66b7
- c297513faa34104fe812a1e59d0f98fb6fe741d2ddb2fc424dce33ee175a8c7e
- c332f3148d35b98d5b9aebb25f7642bf2315476edf8640f4e49a04bff7ef1992
- c7049f22ae5ea4adfba9a137ee331874fee567dcfca6ef04cddbd520d7b00ece
- cafb2d43814edf00a88b69ef44a0cdd7f8217b05132638bfe62a633b021be963
- ce3b09833cb88e8dda668604a50dee535f3ab3f9edc258e2a2f389064065d1b9
- cf374b923e49a731b035faae8fb0756e71d8377dc4b584fc51595320b1e5bc23
- d132b6b606284363684e9ed72fa516c751c5a5447a7af78b803b368a68e1319b
- d441fadd2e5dfbf526802b611391a7433578c8b507757bd606f873dde76ba290
- d539ced1656cbeda5fb3c9fa7a7dd15d379543877921fb6b988fe1ff0e5cb65a
- d8a7d38189c1b552ba07b3c12536c9cb9f7291161180937c08d28c736e3a84bc
- dcc3e88eabf7700facf18c6f905d21c1450e38f17190d38afabfb5aede2d2aab
- de0461d80b3a5986cd7a290620f4e1096b86a80ecb72e5033af944a0a368e374
- e0366f1f6d7d396f6ef06b8398f9d899c94757449ee32b45ff855d77d1442256
- e10a1bde9ed99785982416b20443e1c9387375876cf21887f6470f32d29eeac6
- e597f985a19237355dd489fa6eb95fdcb22b6d1a5125574aceb1c82e42057e72
- e5a9c5284062d9862dba21c860b32d6f58559175af193c052d0d968a17336d98
- f0f57933cba2b43988458cab4e386e4949902c23df723a97eb8da53bd8d4a49d
- f2c4f0c152acbb4a8e575e6095fc84b6df932e114c4f2a32a69d1ed19c1a55f7
- f4c3fecde4a9a5557fe1eca14b6b051aeb3c282780d51163ad4e11ef32454d20
- f89b07f4043c0bccd8537ed6a24f15932b9f70cc10743e022487bee62c075f98
- fa0aefa912e04ffcb1895e917d24372816c9da6f827b36079eaa115a0349dc0a
- faf630469655fcddb34a6bb2f24a5857bd36fd463760fe7643dbeb3f080b9a72
- fba6378aaf31225825c21cc7b06e1e8a408102bdba7a18a1b3d84b23cfe08018
- fbcf1356f2c11fe73efe69c1eba77a62ae742c935f3232dbed77657408a06933